We last looked at an inside threat – now let’s consider some external threats:
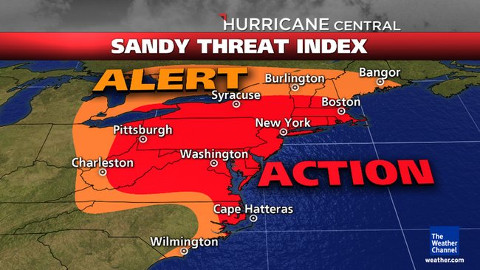
Dennis the Weatherman is a proxy for the threats that nature presents. Superstorm Sandy is a recent example of the power of weather. Some places received over a half meter of rain in less than 24 hours, as well as high winds. The combination of flooding, storm surge, high winds and downed trees wreaked havoc on businesses and data centers over an extended area.
Superstorm Sandy highlighted many factors around disaster preparedness. Some companies were able to fail over to geographically remote data centers and continue operations with minimal disruption.
Some companies had mixed experiences. One of the best examples is Peer 1 Hosting – their data center was well above the flooding and they had backup generators. Unfortunately, their diesel fuel tanks for the backup generators were in the basement… They had to form a “bucket brigade” to carry diesel fuel up 17 flights of stairs.
Other companies were simply down. Without power or network connectivity there was nothing they could do. Worse, their datacenters may have been flooded and the equipment damaged or destroyed. Worst case would be a flooded datacenter without adequate offsite disaster recovery or even backups; some companies went out of business.
In addition to hurricanes, you have to worry about flooding, tornadoes, fire and wildfire, blizzards, and earthquakes.
The good news is that the computer systems in the basement of a flooded data center which is burning down in the middle of an earthquake are not likely to be hacked…
Yes, weather is a clear and present danger to system integrity. Plan accordingly. PLAN accordingly! Exactly what will you do if your data center is under water and located in the middle of an entire region of downed trees with roads blocked by thousands of people trying to escape. And maybe even Starbucks closed!